Early Warning Intelligence — How to predict cyber attacks?
Introduction
When you read any CTI report, you will often find that it answers more or less the same questions. How did the attacker get into the system? What were the steps following the initial compromise? And what is the impact?
But is it possible to predict a cyberattack? The methods used for that today are based on several assumptions. To explain simply; We assume that a threat actor will repeat the same post-compromise behaviour we observed. But in my opinion, we are focusing on the wrong part of the “kill chain”.
In this article, instead of focusing on post-exploit indicators, we will look at how to construct an early warning system by observing the preparation stages.
What is a Prediction?
Let’s start by defining what we should expect from a “prediction”.
- Time period in which the attack is expected to occur
- Type of the attack (e.g: malspam, phishing, exploitation)
- Certainty / confidence (e.g: with 60% chance)
- Threat duration
- Observables (if available)
- Signals used to make the prediction
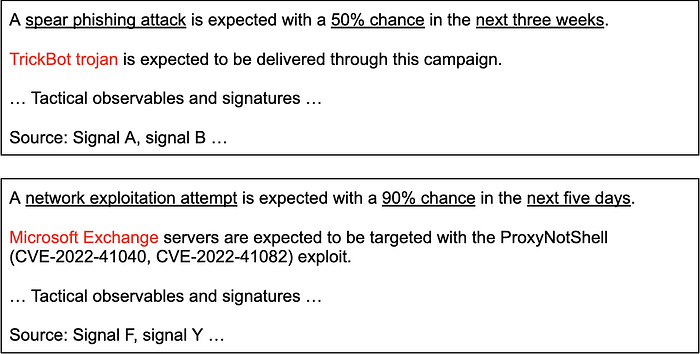
Sample memo:
A Closer Look at Initial Access Vectors
When we read through the CTI reports, we see that there are several initial access vectors that are frequently used by cybercriminals.
- Network service exploitation
- Malspam campaign
- Spear phishing
- Credential attacks (wordlist attacks)
- Buying access
This is also beautifully illustrated in the IAB Landscape chart prepared by the CuratedIntel community.
Since these are preparatory stages, we can assume that an attack of a certain type will only occur when the corresponding conditions are met.
The question we must now ask is: which of these stages can we observe from the outside? And how?
Identifying Observation Opportunities
If we can deduce patterns about the preparatory phases, we can use them as an opportunity for observation. For instance, the main goal of network service exploiters is to hijack as many devices as possible. Therefore, they generally target widely used network protocols such as Email, file sharing, VPN.
In addition, most actors who do this work do not have the skills to develop the exploit code themselves. Therefore, they use ready-made exploit modules published by companies such as Metasploit, Cobalt Strike, or other security researchers.
Using these patterns, we can develop the following signals to predict an NSE campaign.
- Signal 1: A new vulnerability of a widely used network service has been discovered.
- Observe: NVD, CVE
- Signal 2: The exploit module for the given vulnerability has become available.
- Observe: Rapid7, Exploit-db, Github, Cobalt Strike, Dark web
- Signal 3: A new exploit code has become available for a known vulnerability.
- Observe: same as Signal 2
- Signal 4: An exploit kit has begun to be advertised in crime markets.
- Observe: Dark web
- Signal 5: An exploit has been observed in the wild.
- Observe: CISA, Greynoise
The same process can be done for other vectors too. Let’s take malspam as another example.
Malspam is another type of vector in which actors go after quantity and are very opportunistic. For that reason they’re often delivered through cracked software or ads.
Using these patterns, we can develop the following signals to predict a malspam campaign:
- Signal 1: A popular game or software has become available on torrent websites.
- Observe: Popular torrent sharing websites
- Signal 2: A new season of a popular series has been released.
- Observe: News, movie sharing websites
- Signal 3: There is an increase in the activity of a certain botnet/trojan family.
- Observe: Malware bazaar, C2 feeds
- Signal 4: New distribution hosts are identified for a certain botnet/trojan family.
- Observe: URLhaus, Virustotal
- Signal 5: Crack of a commercial RAT has been shared in the forums.
- Observe: Dark web
- Signal 6: New crypter has been shared publicly.
- Observe: Dark web, Github
You can also find some other examples in this blogpost.
Building the Early Warning System
If you have developed some observable signals with the above process, now it’s time to construct the early warning system.
This process is similar to creating a mathematical equation where each of the signals we defined is a boolean variable (0 or 1). We multiply each of our events by a weight value, add them together or combine them with logical operators, and generate an alert when it exceeds a predefined threshold.

EWS for network service exploitation:
if (S1*0.1 + S2*0.3 + S3*0.1 + S4*0.3 + S5*0.3) > 0.5
- Signal 1: A new vulnerability of a widely used network service has been discovered. (Weight = 0.1)
- Signal 2: The exploit module for the given vulnerability has become available. (Weight = 0.3)
- Signal 3: A new exploit code has become available for a known vulnerability. (Weight = 0.1)
- Signal 4: An exploit kit has begun to be advertised in crime markets. (Weight = 0.2)
- Signal 5: An exploit has been observed in the wild. (Weight = 0.3)
EWS for malspam campaigns:
if (S1*0.1 + S2*0.3 + S3*0.1 + S4*0.3 + S5*0.3 + S6*0.3 + S7*0.2) > 1.0
- Signal 1: A popular game or software has become available on torrent websites. (Weight = 0.4)
- Signal 2: A new season of a popular series has been released. (Weight = 0.1)
- Signal 3: There is an increase in the activity of a certain botnet/trojan family. (Weight = 0.3)
- Signal 4: New distribution hosts are identified for a certain botnet/trojan family. (Weight = 0.2)
- Signal 5: Crack of a commercial RAT has been shared in the forums. (Weight = 0.3)
- Signal 6: New crypter has been shared publicly. (Weight = 0.2)
Weights and thresholds are subjective to your organisation and type of attack. You may experiment and find out what works for you best.
See you in another article!
